for the content of PeterJockisch.de:
Peter Jockisch
Address
Peter and Erika JockischHabsburgerstraße 11
D-79104 Freiburg i.Br.
Germany
Email: info@peterjockisch.de
OpenPGP key
6582 1C57 E0EE 47DA C2CA DF62 4AD7 371A C6E6 BE9FDear Site Visitors,
Thank you for your interest! I appreciate any feedback and constructive criticism.
If you would like to establish contact with me, it is advisable to first read the information in the question column, please. Unfortunately, a guaranteed answer cannot be given.
Prefered communication medium: Cryptographically signed E-Mail
Currently, the effective protection that can be achieved with publicly available cryptographic technology is highly questionable. Advanced computer technology is likely to be kept out of the public domain in order to keep the intelligence services of the rulers at the forefront of computing power. In addition, software and hardware backdoors probably exist. Officially recommended standardized encryption methods may have inherent mathematical weaknesses: Why should the intelligence services of the Western and Eastern hemispheres recommend and give away self-developed secure algorithms whose use would make their central work, interception and industrial espionage, impossible?
The higher-ranking organisations of those families who stand above the law most probably have an incomparably strong calculating power, which normal users have little to oppose. However, some of the potential attackers under the law can be fended off. The communication security can be increased at least within a certain framework, by consistent use of cryptographic signing.
All my e-mails are always signed cryptographically, with PGP/MIME or a separate signature. I never send unsigned e-mails without any exception. Signatures need to be verified, for example with GnuPG GNU Privacy Guard, www.gnupg.org, MS Windows version: www.gpg4win.org. I only use the key listed in the imprint. PeterJockisch.de is the only official source for my key.
Signature verification with OpenPGP and GnuPG
To view a name and a cryptographical checksum, is not sufficient. For the authentication, the signature must be verified. After the initial activation, modern e-mail agents fully and automatically verify in the background.
For the qualified electronic signature, most often, only hardware-based (chipcard) class-3-certificates, certified by legally recognized CAs are accepted by law. However, the required hardware and software infrastructure (available card readers, supported operating system, e-mail agent, software) is throughout of proprietary nature. This means not checkable and visible and thus, risky under security aspects. If attached to your email, I maybe will use such public X.509- or OpenPGP certificates with my MUA – However, I myself do not sign with such certificates
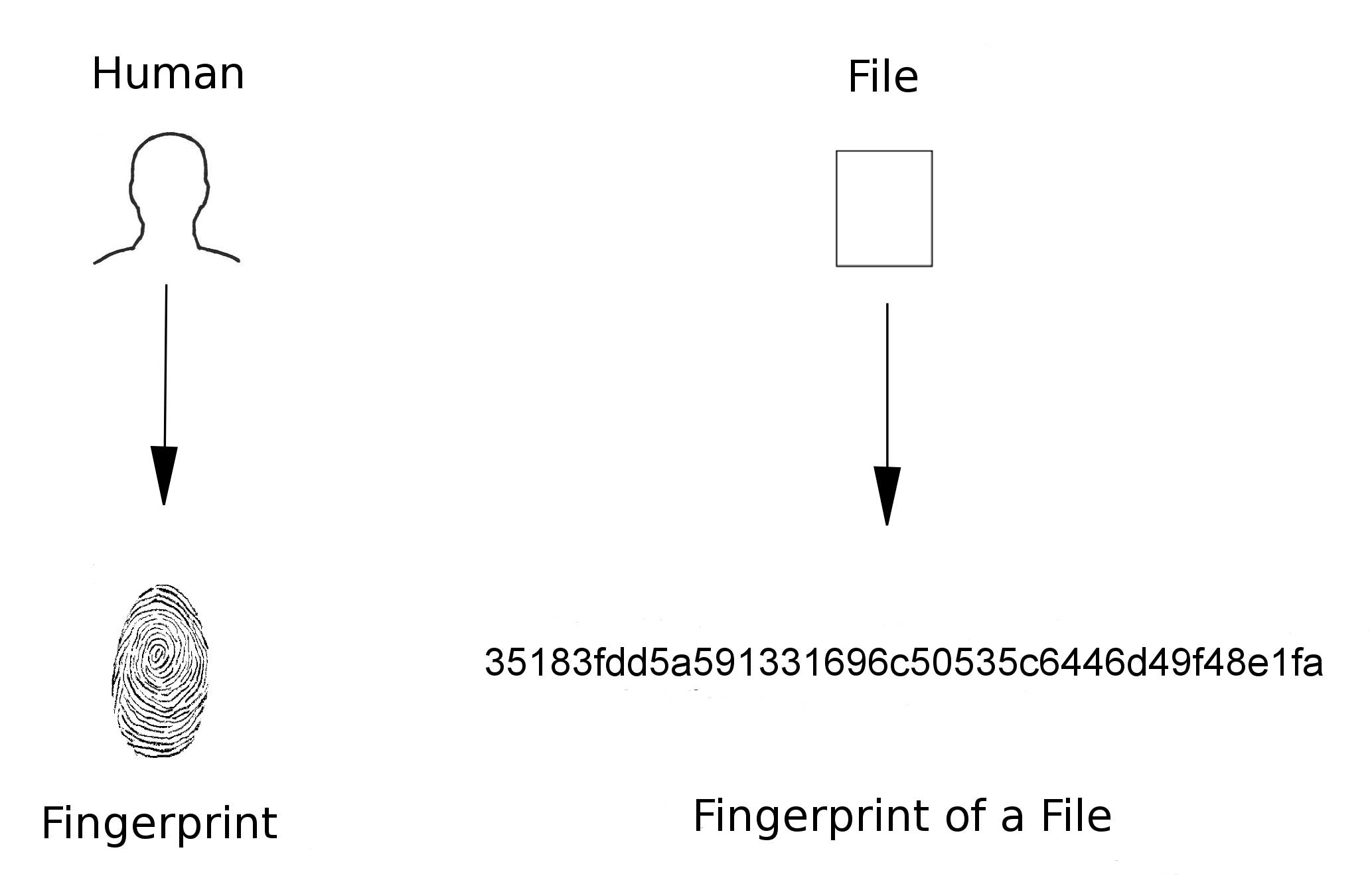
Cryptographical checksums as alternative proof of authenticity
Some recipients are not familiar with practical encryption and signing, or they have no possibility to use it in their country. In these cases, in addition to the signed e-mail, I write the message seperately in a “.txt” or “.pdf” file and publicize its checksum in the checksum blog section on PeterJockisch.de, combined with the date of dispatch, sending time and initials indicating the document.
Checksums for files can be created with a single right mouse click, for example with Free Software like Cyohash or Jacksum. More information about the application possibilities can be found in the introductory article “Practical application of cryptographic checksums”.
For verification, the checksum of the attached ".txt" or ".pdf" file must first be formed. You can then check the checksum blog area of PeterJockisch.de to see whether there is an entry with the corresponding checksum for the e-mail date in question. Checksums of my e-mails are published there and only there, nowhere else:
http://www.peterjockisch.de/blog_en/checksums-blog.html.
My e-mail texts do not contain any data on the checksum. That would be completely senselessly. Everyone could write an arbitrary file and subsequently copy a checksum of the blog section into the e-mail text.
SSL/TLS certified site sections will follow.
No telephony, no mobile telephony, no fax
Principally, on a business level, I do not communicate by telephone which is unsuitable for proof of identity. With regard to the authenticity of spoken language, it is suggested to everyone, to inform about “Adobe Voco”, for example by a Google search for “Adobe Voco”.
Telephone information is principally not given. I do not own a mobile phone and no fax machine and I deny respective contracts or offers.
Due to telephony being unsuitable for proof of identity and the high risk of impersonation, I only conduct phone calls with immediate family, using landline network only. I principally do not use mobile telephony, SMS or fax.
In many fields (energy production, communication, health etc.), there are beneficial free technologies, methods and procedures, which are not permitted, which are to the present day held blocked. However, future generations will be able to use these technologies and methods.The currently allowed telephone mobile communication technologies have inherently numerous critical aspects, which are documented in numerous films and articles, amongst others in the following lectures: English: Youtube playlist “Mobile Phone Criticism” • German: Youtube playlist “Mobilfunkkritik” • “Mobilfunk – die verschwiegene Gefahr (5. überarbeitete Auflage mit aktuellem 5G-Sonderteil)”, 2019, Klaus Weber (PDF, 40 pages)
Further information are also available on diagnose-funk.org and www.chemtrail.de, among others in the “Mobilfunkbroschüre” of the comprising information site Chemtrail.de: Dokumente → Dokumentenarchiv (PDF‘s+Doc‘s).
The national and international websites of the link lists there, “Links” and “Links zu”, as well as numerous other websites, also including the column “Cell Phone Dangers” of the news portal rense.com, contain detailed information on the subject.
Critical illustrations on the cell phone technology which is permitted by the rulers are available at http://www.deesillustration.com.
I do not engage in discussions, neither on the telephone nor on site. Who has a say may do that in written form, preferably via e-mail. Unfortunately, an answer guarantee cannot be given.
No representatives, no employees
I neither have representatives, nor assistants nor employees who speak for me. This will not change in the future. I do not offer any job.
No advertising, no Advertsising E-mails or Letters, no Newsletters, no Product Advertising
Non of my websites sends advertising e-mails or newsletters. I principally do not use newsletters, instead I use consistently RSS news tickers which have numerous advantages over e-mail newsletters. Introductory article: „Keep up with the News with RSS Feed Readers.“
I principally do not write readers' letters, and do not send any advertising e-mails, advertising letters, or news letters.
All information are offered exclusively “passively” on my own official websites. Current news and notifications can be read in news sections and can be obtained via RSS news tickers publicized on my official websites
All websites recommended by me are exclusively listed on my own websites. I do not practise banner exchange.
I neither use Facebook nor Twitter nor MySpace, no eBay, no PayPal, or any other similar services.
General remarks on precautionary measures in e-mail communication: Fraudsters, e-mail spam senders (WP article “Spamming”) and discrediters/eputation-damaging persons often use real e-mail addresses from the Internet to underpin their credibility. The sender name and sender address of an e-mail can easily be forged. In addition, the utmost caution is required when attachments such as .zip files are attached to alleged invoices, credits, declarations of love, faxes, etc., which are intended to lead to ill-considered action and opening of the attachment as a result of emotional turmoil. Forwarding a suspicious email to a third party for analysis is also risky, as it could put you on the list (blacklists) of senders of fraudulent and spam emails fully automatically (via email delivery system analysis procedures) and discredit your own email address. In general, every step should be carefully planned in such cases, as otherwise you run the risk due to ill-considered reactions that those affected by the identity theft (WP article “identity theft”) could also take legal action against you because of damage to their reputation.
All websites recommended by me are exclusively listed on PeterJockisch.de as well as on PeterJockisch.com. I do not practise banner exchange. “Business propposals” of any kind are unwanted.
No Collection of Donations, no Appeals for Donations
I don't collect donations: I don't write any donation emails and I don't call for such actions. I do not have a donation function for myself or for my internet pages. I do not send any advertising material for third parties, nor do I send any donation-call e-mails or letters for third parties.
This information is given in order to exclude possible free riders.
Official Websites and Publication Platforms, Technical Aspects
As a matter of principle, I only publish on Internet pages of which I am the sole owner. My webhoster service provider is Hetzner Online GmbH, hetzner.de (English version). All my webpages and contents are published exclusively via this webhoster. An exception to this are only my user account at Archive.org, “www.peterjockisch.de”, under which only copyright-free documents are published, and my Youtube channel “Peter Jockisch”.
Here are the only authorized websites of Peter Jockisch where photos, videos and audio files as well as articles are published:
| Domain, URL | Theme | Language |
|---|---|---|
peterjockisch.de |
Personal page |
EN / DE |
| peterjockisch.com | currently empty | EN / DE |
All listed brand names, trademarks and work titles are the property of their respective owners
Imprint • Privacy Statement • Biographical Notes